by Andy Jenkinson
Share
by Andy Jenkinson
Share
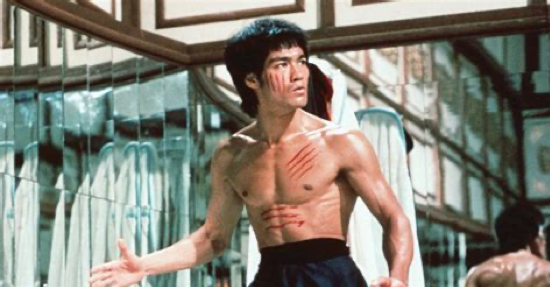
Despite recent National Security warnings from National Cyber Security Centre, key domains linked to critical infrastructure—energy, communications, and even government—show inconsistent and in many cases unsecure and inadequate DNS security postures.
DNSSEC, a foundational protection against spoofing and redirection attacks, remains only partially deployed or misconfigured.
That is not a theoretical weakness; it is a practical doorway.
EDF and National Grid have been repeatedly informed over the last several years, yet have knowingly ignored and remained wholly unacceptably exposed.
Organizations under the protective umbrella of MI5 appear better at issuing warnings than enforcing baseline cyber hygiene.
When companies like National Grid and EDF exhibit avoidable gaps for several years, the issue is systemic, not incidental.
The contradiction is stark: while officials brief on advanced AI threats, basic, well-understood protections remain inconsistently and insecurely applied.
National security is not undermined by hypothetical tools alone, but by neglected fundamentals.
This is not merely suboptimal—it is unacceptable.
A nation cannot claim preparedness for emerging threats while leaving its digital front door ajar.
Our Intelligence Agencies, these companies, and our government should be thoroughly ashamed of themselves.
STAY IN THE LOOP